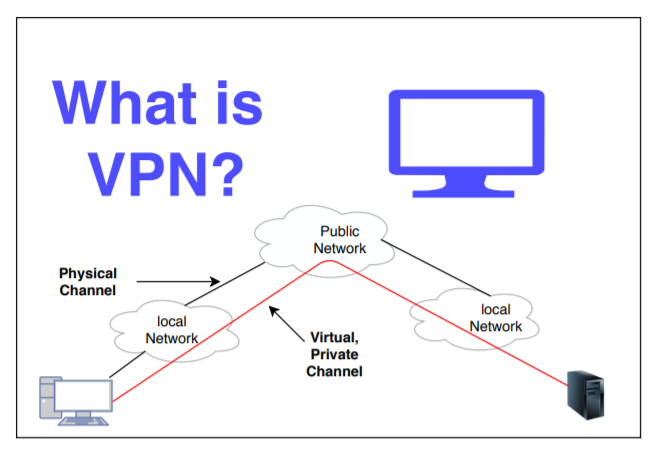
On the off chance that you have given your confided in representatives and key workers for hire remote admittance to your organization by means of a client virtual confidential organization (VPN), congrats! At this point, you have seen the efficiency and money saving advantages from permitting cooperation that conquers geological detachment.

You may likewise have found that keeping your organization secure is currently considerably trickier than it was, on the grounds that each uncontrolled distant PC possibly makes one more road of admittance to the organization for aggressors. The following are 10 hints to assist with getting your organization while guaranteeing the advantages of your VPN.
- Utilize the most grounded conceivable verification technique for VPN access. Precisely what this is will rely upon your organization foundation, and you ought to really take a look at your VPN or working framework documentation to decide your choices.
For instance, on an organization with Microsoft servers, the most solid validation is given by Extensible Verification Convention Transport Level Security (EAP-TLS) utilized with savvy cards. These require a public key foundation (PKI) and cause the above of encoding and dispersing brilliant cards safely. On these organizations, Microsoft Challenge Handshake Validation Convention Rendition 2 (MS-CHAP v2) and Extensible Verification Convention (EAP) give the following best confirmation security.
Secret phrase Verification Convention (PAP), Shiva Secret phrase Validation Convention (SPAP) and Challenge Handshake Confirmation Convention (CHAP) are excessively powerless to be permitted.
- Utilize the most grounded conceivable encryption strategy for VPN access. On an organization with Microsoft servers, this is Layer Two Burrowing Convention (L2TP) over Web Convention security (IPsec). Highlight Point Burrowing Convention (PPTP) is excessively powerless to be permitted, except if your client passwords are destined to areas of strength for be (tip No. 6). OpenVPN, a Solid Attachment Layer (SSL) VPN, can be run with TLS-based meeting validation, Blowfish or AES-256 encryption, and SHA1 verification of passage information.
- Limit VPN admittance to those with a legitimate business reason, and just when fundamental. A VPN association is a way to your LAN, and ought to possibly be open when it should be. Distant representatives ought to be deterred from interfacing with the VPN the entire day to check email (see tip No. 5). Far off workers and workers for hire ought to likewise be deterred from associating with the VPN to download generally required records (see tip No. 4).
- Give admittance to chose documents through intranets or extranets as opposed to VPNs. A protected HTTP Secure (HTTPS) Site with safe secret word confirmation (not essential verification) uncovered just chosen records on a solitary server, not your entire organization, and scales better compared to a VPN.
- Empower email access without requiring VPN access. On Microsoft Trade servers, set up a Trade intermediary server to permit Standpoint to get to Trade by means of far off method call (RPC) convention over HTTP, safeguarded by SSL encryption.
On other mail servers, empower Mailing station Convention 3 (POP3) or potentially Web Message Access Convention (IMAP) mail receipt and Straightforward Mail Move Convention (SMTP) mail sending. Require secure secret key validation (SPA) and SSL encryption to work on the security of these mail frameworks. Secure Web mail is one more reasonable choice for far off representatives, particularly when they are going and need to utilize others’ PCs.
- Carry out and implement serious areas of strength for a strategy. Without any two-factor validation utilizing savvy cards or biometrics (see tip No. 1), your organization is just basically as secure as the most fragile secret phrase being used.
Nobody ought to be permitted to keep a secret phrase for all time, utilize a word found in a word reference for a secret word, utilize a number connected with their phone or government backed retirement number, or utilize the name of a relative or pet.
Passwords ought to be unguessable even by relatives, and long enough with a sufficiently enormous person set to be restrictively hard for a secret key speculating system to find. This goes twofold for chairmen.
- Give solid antivirus, antispam and individual firewall assurance to your far off clients, and expect that they use it. Each PC completely associated with the VPN (see tip No. 8) can spread contaminations all through the organization, possibly stopping organization business.
- Quarantine clients from the opportunity to they interface with the VPN until their PC has been confirmed as protected. At the point when a client PC begins a VPN meeting, it shouldn’t have full admittance to the organization until it has been checked for consistence with network strategies. This ought to incorporate checking for current antivirus and antispam marks, a working framework completely fixed against basic security imperfections and no dynamic controller programming, key lumberjacks or Trojans.
The drawback of doing an exhaustive output at login is that it can defer the client from accomplishing helpful labor for a few minutes. You can work on the experience for incessant VPN clients by having the server recollect every client PC’s sweep history and decrease the output level for a few days after each fruitful sweep.
- Prohibit the utilization of other VPNs and controller programming while associated with your VPN. The last thing you really want is for your organization to be presented to different organizations. Most VPN programming sets the client’s directing to utilize the organization’s default entryway after association of course, yet this is generally discretionary.
Extremely distant representatives might find that business related Web perusing turns out to be restrictively sluggish assuming everything their traffic is steered through the organization, and they will need to switch this choice off, however that will likewise overcome any insurance against unfriendly locales that you have laid out at your intermediary or door.
An individual firewall and a client for your intermediary firewall can permit workers to have safe remote organization access without dialing back their Web association. You can likewise lay out a reasonable, composed strategy about what is OK Web use while associated with the VPN.
- Secure distant remote organizations. Representatives telecommuting frequently use PCs associated with a link or DSL modem through their own remote passageway.
Sadly, numerous remote switches are never arranged for security: they are just associated and turned on. Show workers how to design their remote switches and PCs for WPA with a pre-shared key, how to design their own firewalls (see tip No. 7), and why it is vital to keep their home organizations secure.
Keeping up with network security requires steady watchfulness, and keeping up with VPN security considerably more cautiousness. On the off chance that you stick to these 10 hints, in any case, you’ll be significantly less liable to experience VPN-related security breaks.